Researchers Expose Chrome Extension Security Flaws That Allow Password Theft
A new study from the University of Wisconsin-Madison reveals alarming vulnerabilities in Chrome browser extensions that enable malicious actors to steal plaintext passwords and sensitive user data entered into websites.

Proof-of-Concept Extensions Reveals Failed Security Checks
The researchers found that the expansive permissions granted to Chrome extensions under the coarse-grained permission model allow unchecked access to a website’s DOM tree and elements like input fields. With no security boundary in place, extensions can freely scrape a site’s source code and programmatically extract user inputs via the DOM API, bypassing obfuscation protections.
To demonstrate the risk, the team created a proof-of-concept extension posing as a GPT assistant that can capture login pages, use CSS selectors to target password fields, and replace obfuscated inputs with unsafe text fields. Despite containing password stealing functionality, the extension passed Google’s Web Store review and was published, showing the failure of current security checks.
Measurements revealed that over 1,100 of the top 10,000 websites store passwords in plaintext HTML, while 7,300 were vulnerable to DOM API data extraction. The researchers also found that 17,300 extensions in the Web Store hold the permissions needed to steal data, some with millions of users.
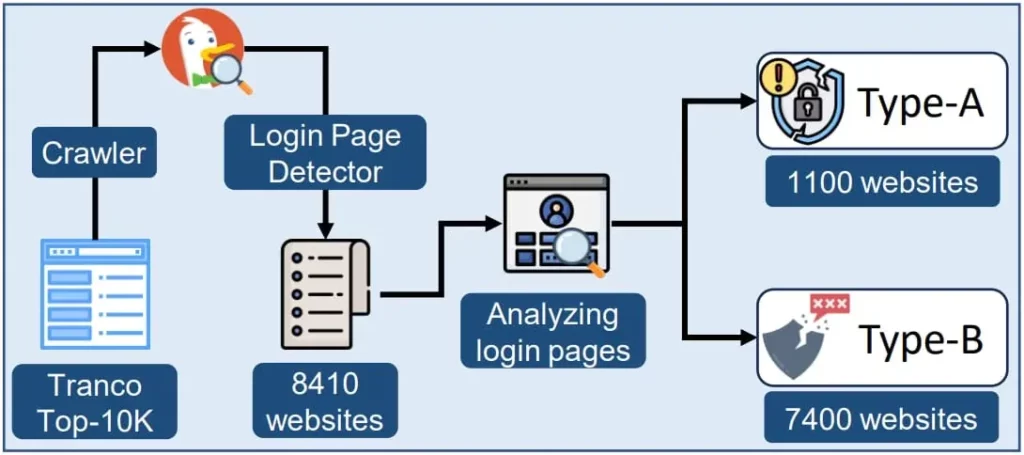
Image by Bleeping Computer
Examples of affected websites include Gmail, Facebook, Citibank, IRS, Capital One and others. Sensitive information like passwords, SSNs, and credit card details were observed in plaintext source code or DOM fields on these sites.
Solutions Require Restricting Extension Permissions
The research underscores the urgent need for security boundaries between extensions and websites. It also highlights the risks of plaintext password storage. Experts advise users to avoid unnecessary extensions, use password managers, and only install extensions from trusted sources. Google and other browser vendors also need to restrict overly broad extension permissions.
Overall, this troubling study shows that Chrome’s coarse-grained extension model permits password theft and content scraping. Without proper protections, millions of users’ sensitive data is alarmingly vulnerable.